Contactless pre-bond TSV fault diagnosis using duty-cycle detectors and ring oscillators | Semantic Scholar

Hardware and Information Security Primitives Based on 2D Materials and Devices - Wali - 2023 - Advanced Materials - Wiley Online Library

High-Level Approaches to Hardware Security: A Tutorial | ACM Transactions on Embedded Computing Systems

Contactless pre-bond TSV fault diagnosis using duty-cycle detectors and ring oscillators | Semantic Scholar

Practical fault resilient hardware implementations of AES - Sheikhpour - 2019 - IET Circuits, Devices & Systems - Wiley Online Library

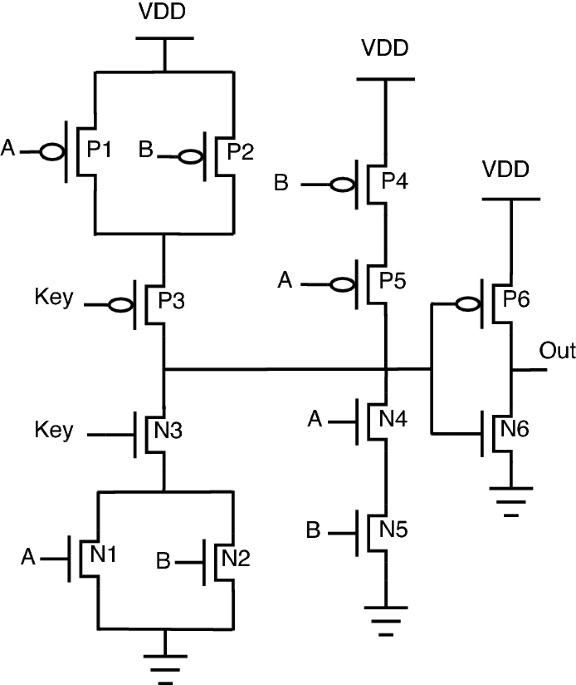
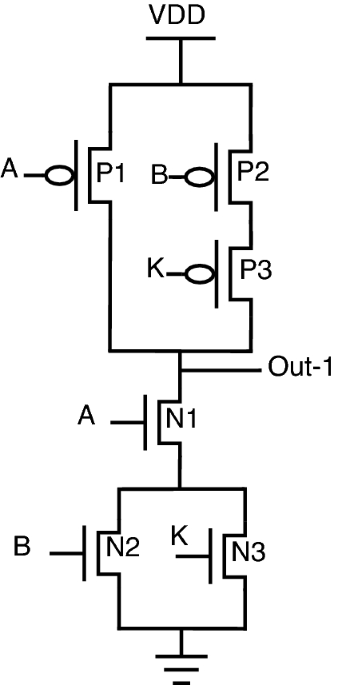
Hardware obfuscation of AES IP core using combinational hardware Trojan circuit for secure data transmission in IoT applications - Chhabra - 2022 - Concurrency and Computation: Practice and Experience - Wiley Online Library
![PDF] Parity-Based Concurrent Error Detection Schemes for the ChaCha Stream Cipher | Semantic Scholar PDF] Parity-Based Concurrent Error Detection Schemes for the ChaCha Stream Cipher | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1f4bd3d0625e25e81f4ba75cc0b1237ea7c11e46/2-Figure1-1.png)
PDF] Parity-Based Concurrent Error Detection Schemes for the ChaCha Stream Cipher | Semantic Scholar
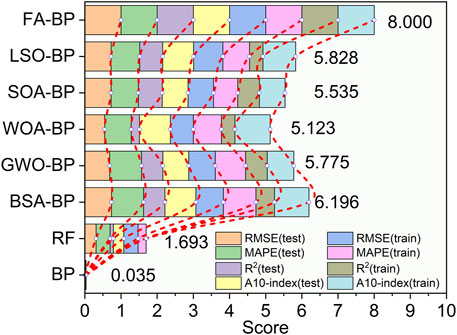
Frontiers | A Comparative Study of Six Hybrid Prediction Models for Uniaxial Compressive Strength of Rock Based on Swarm Intelligence Optimization Algorithms